7 start with I start with I

Tekobbe’s methods for analyzing and understanding Indigenous knowledges online center Indigenous storytelling and “thick” (broad, deep, and complex) Indigenous meaning-making. Employing this thickness to interpret Indigenous knowledge ways resists the settler-colonial logics that tend to flatten complex Indigenous concepts into one-note representations of racial stereotypes. Native Americans’ use of social media and digital platforms to support social movements uniquely constructs Indigenous identities as living, producing, and culture-making people, which confronts the commonplace, one-dimensional narrative that Indigenous North Americans either live in isolation or are people of history resigned to the long-forgotten past. Tekobbe’s methods are applicable to additional online research to break through Western paradigms of oppositional critique, the colonial power matrix embedded in hierarchical and taxonomical classification systems, and participant objectification.
Indigenous Voices in Digital Spaces offers new methodological and epistemological opportunities to explore digital communities and technologies, problematizing conventional Western critique. This book is useful to instructors in Indigenous studies, internet studies, digital literacies, cultural studies, and communications, as well as Indigenous and internet studies researchers.
The most extensive account yet of the lives of cybercriminals and the vast international industry they have created, deeply sourced and based on field research in the world’s technology-crime hotspots.
Cybercrime seems invisible. Attacks arrive out of nowhere, their origins hidden by layers of sophisticated technology. Only the victims are clear. But every crime has its perpetrator—specific individuals or groups sitting somewhere behind keyboards and screens. Jonathan Lusthaus lifts the veil on the world of these cybercriminals in the most extensive account yet of the lives they lead, and the vast international industry they have created.
We are long past the age of the lone adolescent hacker tapping away in his parents’ basement. Cybercrime now operates like a business. Its goods and services may be illicit, but it is highly organized, complex, driven by profit, and globally interconnected. Having traveled to cybercrime hotspots around the world to meet with hundreds of law enforcement agents, security gurus, hackers, and criminals, Lusthaus takes us inside this murky underworld and reveals how this business works. He explains the strategies criminals use to build a thriving industry in a low-trust environment characterized by a precarious combination of anonymity and teamwork. Crime takes hold where there is more technical talent than legitimate opportunity, and where authorities turn a blind eye—perhaps for a price. In the fight against cybercrime, understanding what drives people into this industry is as important as advanced security.
Based on seven years of fieldwork from Eastern Europe to West Africa, Industry of Anonymity is a compelling and revealing study of a rational business model which, however much we might wish otherwise, has become a defining feature of the modern world.

Poster’s critique develops through a series of lively studies. Analyzing the appearance of Sesame Street’s Bert next to Osama Bin Laden in a New York Times news photo, he examines the political repercussions of this Internet “hoax” as well as the unlimited opportunities that Internet technology presents for the appropriation and alteration of information. He considers the implications of open-source licensing agreements, online personas, the sudden rise of and interest in identity theft, peer-to-peer file sharing, and more. Focusing explicitly on theory, he reflects on the limitations of critical concepts developed before the emergence of new media, particularly globally networked digital communications, and he argues that, contrary to the assertions of Michael Hardt and Antonio Negri, new media do not necessarily reproduce neoimperialisms. Urging a rethinking of assumptions ingrained during the dominance of broadcast media, Poster charts new directions for work on politics and digital culture.

A complete history and theory of internet daemons brings these little-known—but very consequential—programs into the spotlight
We’re used to talking about how tech giants like Google, Facebook, and Amazon rule the internet, but what about daemons? Ubiquitous programs that have colonized the Net’s infrastructure—as well as the devices we use to access it—daemons are little known. Fenwick McKelvey weaves together history, theory, and policy to give a full account of where daemons come from and how they influence our lives—including their role in hot-button issues like network neutrality.
Going back to Victorian times and the popular thought experiment Maxwell’s Demon, McKelvey charts how daemons evolved from concept to reality, eventually blossoming into the pandaemonium of code-based creatures that today orchestrates our internet. Digging into real-life examples like sluggish connection speeds, Comcast’s efforts to control peer-to-peer networking, and Pirate Bay’s attempts to elude daemonic control (and skirt copyright), McKelvey shows how daemons have been central to the internet, greatly influencing everyday users.
Internet Daemons asks important questions about how much control is being handed over to these automated, autonomous programs, and the consequences for transparency and oversight.
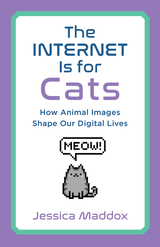
The Internet is for Cats examines how animal images are employed to create a lighter, more playful mood, uniting users within online spaces that can otherwise easily become fractious and toxic. Placing today’s pet videos, photos, and memes within a longer history of mediated animal images, communication scholar Jessica Maddox also considers the factors that make them unique. She explores the roles that animals play within online economies of cuteness and attention, as well as the ways that animal memes and videos respond to common experiences of life under neoliberalism.
Conducting a rich digital ethnography, Maddox combines observations and textual analysis with extensive interviews of the people who create, post and share animal media, including TikTok influencers seeking to make their pets famous, activists tweeting about wildlife conservation, and Redditors upvoting every cute cat photo. The Internet is for Cats will leave you with a new appreciation for the human social practices behind the animal images you encounter online.
READERS
Browse our collection.
PUBLISHERS
See BiblioVault's publisher services.
STUDENT SERVICES
Files for college accessibility offices.
UChicago Accessibility Resources
home | accessibility | search | about | contact us
BiblioVault ® 2001 - 2024
The University of Chicago Press